Zero Trust Solution for Every Device
Trio delivers a Zero Trust solution that enforces MFA, device posture checks, and adaptive policy controls across laptops, mobiles, and cloud apps. With this zero trust security solution, IT admins can prevent unauthorized logins, secure sensitive data, and protect hybrid teams. Designed for SMBs, our zero trust software is simple to deploy and scales as your workforce grows.
Trusted by
Lahore American School
Lahore American School
Lahore American School
Lahore American School
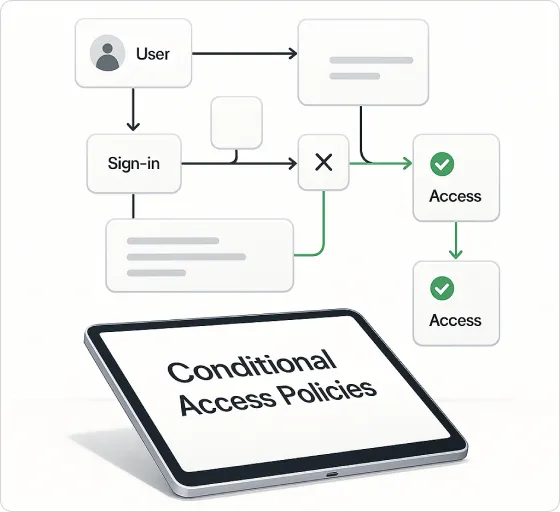
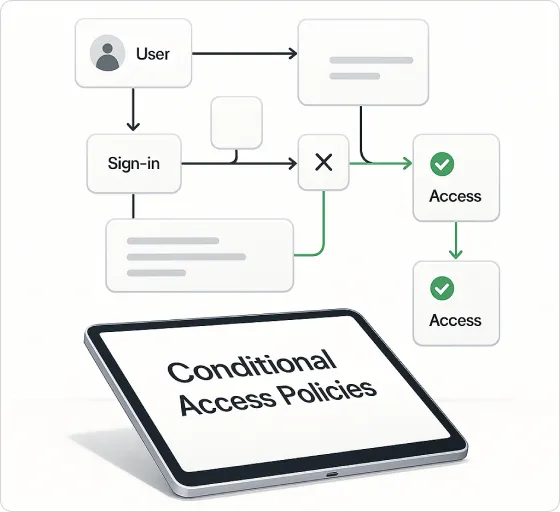
Conditional Access Policies
- Enforce access only when devices meet compliance rules (OS, patches, security posture) through our zero trust security solution.
- Block unsanctioned apps and risky devices from sensitive resources using zero trust software controls.
- Apply policies per role, group, or workload for granular control with a scalable zero trust tool.
Multi-Factor Authentication (MFA)
- Add an extra verification layer to prevent credential theft in a Zero Trust solution.
- Trigger MFA based on risk signals like unusual login location or time.
- Support OTP, push, and biometric methods through zero trust security software.


Context-Aware Controls
- Adapt access policies based on device type, network, or geolocation with zero trust tools.
- Allow trusted in-campus access and enforce stricter rules offsite.
- Dynamically block high-risk sessions without disrupting workflows using zero trust security solutions.


Conditional Access Made Simple
Apply policy-driven access rules that adapt to user, device, and network context—no trust granted by default.

Eliminates Implicit Trust
Every access request is verified, reducing the chance of insider threats or compromised credentials.

Protects Sensitive Data
Granular controls ensure only compliant devices and verified users can reach critical apps.

Adapts to Context
Access is granted based on user identity, device health, and location, minimizing risk.

Strengthens Compliance
Meets security standards with enforced MFA, policy-based access, and continuous monitoring.
Frequently Asked Questions (FAQ)
About Zero Trust
Secure Access for Every User
Protect your apps and data with Zero Trust Access. Enforce MFA, device checks, and policy controls—built for modern, remote, and hybrid teams.