Enterprise Location Tracking & Device Security
Secure every endpoint with real-time location tracking and automated device management deployment across Android, iOS, Windows, and macOS platforms. Transform device security with intelligent geofencing that automatically enforces policies, triggers lost mode protection, and enables conditional access based on precise location data. Trio's unified platform delivers enterprise-grade location tracking with zero-configuration setup designed for resource-constrained IT teams.
Why struggle with fragmented location monitoring solutions?
Centralized location intelligence eliminates tool sprawl while delivering comprehensive device visibility.
Unified Device Visibility
Track live location across all managed endpoints through single dashboard interface. Monitor Android, iOS, Windows, and macOS devices simultaneously with GPS location tracking, Wi-Fi positioning, and cellular tower triangulation. Real-time location tracker provides instant device status updates with coordinate precision down to 10-meter accuracy for critical asset recovery scenarios. Advanced phone location tracking capabilities ensure comprehensive coverage across mobile and desktop platforms.
Automated Security Orchestration
Location-based policies trigger immediate protective actions without manual intervention. Geofence tracking device boundaries automatically enforce compliance rules, initiate remote lock procedures, and execute selective data wipes when devices exit designated secure zones. Conditional access policies leverage geofence tracking to require multi-factor authentication for out-of-bounds access attempts. Real-time phone locator integration enables instant device positioning for security response protocols.
Location Security Automation
Advanced geofencing capabilities with automated policy enforcement and real-time threat response.
Lost Mode Activation
Instantly lock compromised devices and display custom recovery messages with contact information. Lost mode prevents unauthorized access while preserving device location visibility for recovery operations. Supports immediate activation via dashboard or automated triggers when devices exit trusted geofence boundaries. IT administrators can track a phone location even when device is locked, ensuring asset recovery capabilities remain active during security incidents.
Geofence Policy Engine
Create virtual boundaries around offices, warehouses, or restricted areas with drag-and-drop precision. Geofencing tracker monitors entry and exit events, automatically applying security policies based on location context. Supports multiple boundary types including circular regions, polygon shapes, and proximity-based zones.
Conditional Access Controls
Location-aware authentication policies adapt security requirements based on device position. Require additional verification for access attempts outside designated areas, automatically restrict sensitive application access, and enforce VPN connections for remote locations. Integrates with identity providers for seamless authentication workflows.
Remote Security Actions
Execute immediate protective measures when location violations occur. Remote lock functionality prevents unauthorized device usage while maintaining location tracking capabilities. Remote wipe options include selective corporate data removal or complete device reset depending on threat severity and data sensitivity requirements.
Network Security Policies
Intelligent location monitoring balances security needs with device performance. Passive Wi-Fi and cellular positioning reduces battery drain while maintaining accurate phone location services. Configurable update intervals optimize power consumption for different device types and usage patterns. Live location tracking operates efficiently across Android location tracking and iOS deployments without impacting user productivity.
Compliance Monitoring
Automated location-based compliance assessment ensures devices remain within approved geographical boundaries. Generate audit trails for regulatory requirements, monitor policy violations in real-time, and maintain detailed location tracking history for forensic analysis and compliance reporting. Track phone location movements with comprehensive documentation supporting regulatory audit requirements.
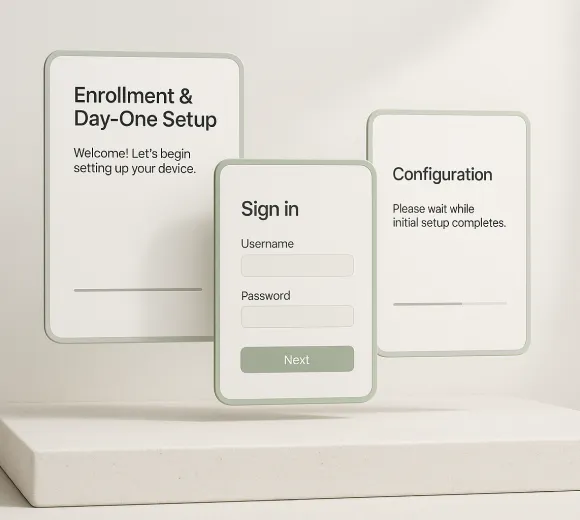
Implementation & Monitoring Process
Streamlined deployment workflow with enterprise-grade capabilities designed for SMB IT administrators. Deploy location tracking across your device fleet in under 30 minutes with our zero-touch enrollment process and automated policy distribution system.
Enrollment & Day‑One Setup
Advanced Security Policy Framework

Automated Response Protocols

Enterprise Android Integration
Comprehensive monitoring platform with advanced analytics, integrations, and compliance automation.

Advanced Reporting Engine
Compliance Framework Automation
Third-Party Integration Hub
Scalable Architecture Platform
Start your 14-day free trial
Join over 4,000+ startups already growing with Trio.